Member-only story
Hack The Box —Legacy Writeup w/o Metasploit
This is the fourth blog out of a series of blogs I will be publishing on retired HTB machines in preparation for the OSCP. The full list of OSCP like machines compiled by TJnull can be found here.
Let’s get started!
Reconnaissance
First thing first, we run a quick initial nmap scan to see which ports are open and which services are running on those ports.
nmap -sC -sV -O -oA nmap/initial 10.10.10.4- -sC: run default nmap scripts
- -sV: detect service version
- -O: detect OS
- -oA: output all formats and store in file nmap/initial
We get back the following result showing that these ports are open:
- Port 139: running Microsoft Windows netbiois-ssn.
- Port 445: running Windows XP microsoft-ds.
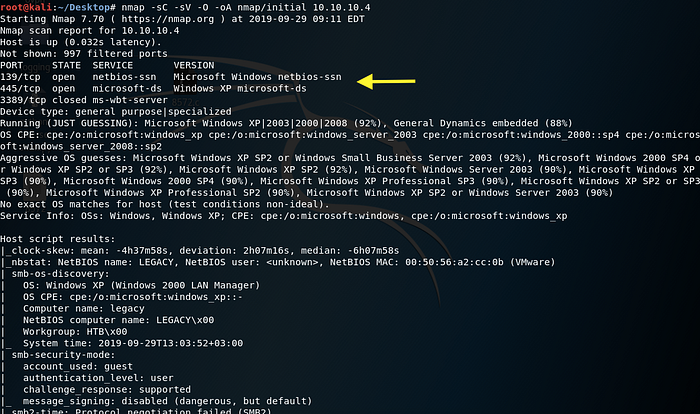
Before we start investigating these ports, let’s run more comprehensive nmap scans in the background to make sure we cover all bases.
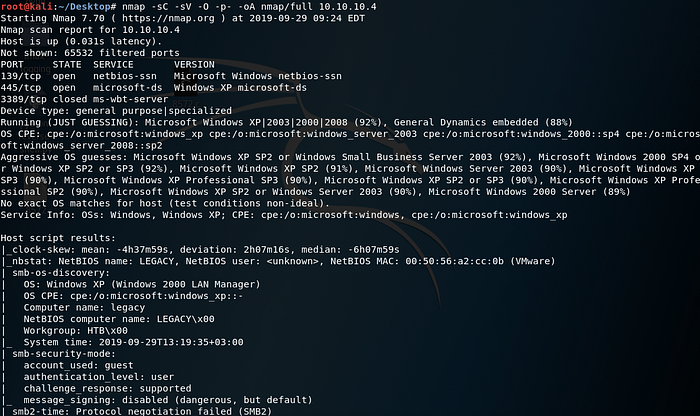
Let’s run an nmap scan that covers all ports.
nmap -sC -sV -O -p- -oA nmap/full 10.10.10.4We get back the following result. No other ports are open.
Similarly, we run an nmap scan with the -sU flag enabled to run a UDP scan.
nmap -sU -O -p- -oA nmap/udp 10.10.10.4We get back the following result. As can be seen, port 137 is open with netbios-ns running on it.
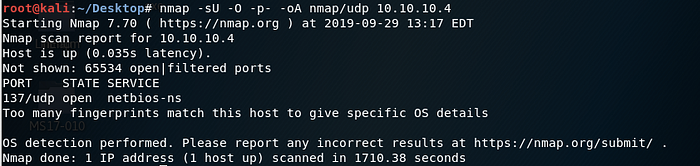
Our initial recon shows that the only point of entry is possibly through exploiting SMB.
